What is Petya Ransomware?
You may have heard about the latest worldwide ransomware attack called Petya. According to Microsoft, reports of the ransomware began spreading across Europe on June 27, 2017. The first infections were in the Ukraine, where more than 12,500 machines encountered the threat. Infections were then observed in another 64 countries including Belgum, Brazil, German, Russia, and the United States.
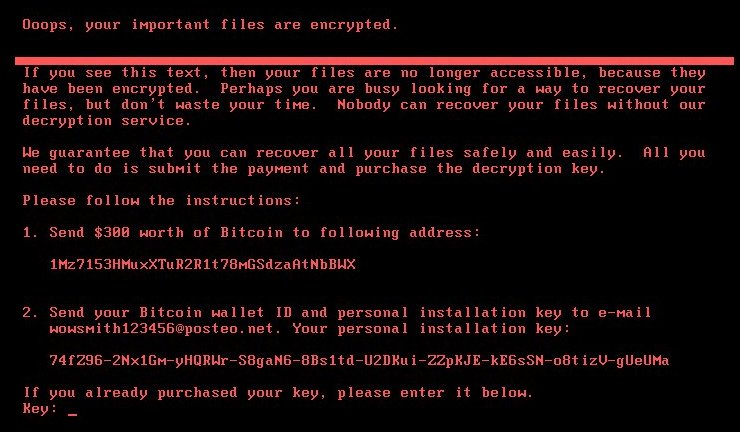
Petya is a nasty piece of malware that, unlike other traditional ransomware, does not encrypt files on a targeted system one by one. Instead, Petya reboots victims computers and encrypts a small portion of the hard drive, which corrupts the booting process, and restricts access to the physical disk. Then Petya ransomware takes over the boot sequence to display a ransom note, leaving computers unable to boot. The ransom note demands $300 in Bit coin and looks like this:
Also, after infecting one machine, the Petya ransomware scans the local network and quickly infects all other machines (even fully-patched) on the same network, using EternalBlue SMB exploit, WMIC and PSEXEC tools.
Actually Petya Isn’t Ransomware, It’s Wiper Malware
Despite the ransom note demanding $300 in Bitcoin, it appears that Petya IS NOT ransomware. Instead, multiple researchers believe that Petya is malicious code that was launched to destroy data rather than collect money.
What Can I Do To Avoid Falling Victim to Petya?
Petya spreads to new computers using the EternalBlue and EternalRomance SMB 1 exploits, which were patched with Microsoft Security Bulletin MS17-010. Therefore, you need to ensure that your operating system has been patched with MS17-010. If you run Windows Update on your system and install all of the critical updates, you will be fine.
Does Office 365 Protect Against Petya Ransomware?
Petya Ransomware is not spred through email, therefore, Petya poses no explicit threat to Office 365 services.
More Information
Keep following us at cFocus Software as we provide you all of the details you need to stay on top of the latest information with Office 365 Government.

